TruCopy is a SCAM
TruCopy.org is a cryptocurrency phishing scam that uses Discord impersonation with typosquatting to steal Bitcoin, Solana, Ethereum, and other cryptocurrencies. This site documents the fraud with blockchain evidence across 8 different blockchains.
Fraudulent Crypto Scam Website
trucopy.org
Multi-Chain Scam Operation
This scam accepts deposits on 8 different cryptocurrencies
BTC
$25K
SOL
$5.8K
ETH
$5
BCH
$0
TRC20
$0
USDT
$0
LTC
$0
DOGE
$0
Active on 3 chains with confirmed thefts. 5+ month operation since September 2025.
Typosquatting Attack Detected
The scammer uses a username nearly identical to a real admin
Can you spot the difference?
REAL ADMIN USERNAME
salmaogs
SCAMMER USERNAME
_salma_ogs
The scammer added TWO underscores: salmaogs became _salma_ogs
Always verify usernames character-by-character before trusting anyone with your money.
How This Scam Works
Typosquatting
Scammer creates a Discord username nearly identical to a real admin, adding underscores.
Fake Platform
Victims are directed to TruCopy.org, a fake trading platform, to deposit crypto.
Multi-Chain Theft
Platform accepts 8 different cryptocurrencies to maximize theft potential.
Rapid Cash-Out
Deposits are moved within minutes to exchange wallets for cash-out.
Total Documented Victim Losses
Based on blockchain transaction analysis of known scam wallets
Confirmed Stolen Amount
$30,869
USD equivalent across Bitcoin, Solana & Ethereum
Theft Summary by Blockchain
| Chain | Wallet | Stolen | Txns | Status |
|---|---|---|---|---|
| Bitcoin | bc1qkh2g...wmgtf | $25,031.80 | 4 | 100% OUT |
| Solana | Cgrr9Rg...oxWJ | $5,833.09 | 5 | 100% OUT |
| Ethereum | 0x3fb84...2529 | $5.01 | 3 | 50% SWAPPED |
| BCH/TRX/LTC/DOGE | Various | $0.00 | 0 | NO ACTIVITY |
| TOTAL STOLEN | $30,869.90 | 12 | ||
Blockchain Transaction Analysis
We traced where the stolen funds go on each blockchain
Bitcoin Money Flow — $25,031.80
February 2026 Update
The scam collection wallet has been linked to a high-volume consolidation wallet that appears to be used to mask the final deposit locations.
TruCopy change addresses appear in transactions from this wallet. This behavior suggests the scammer is attempting to obscure the trail between victim deposits and final exchange cash-out.
Solana Money Flow — $5,833.09
Key Evidence: All 3 cash-outs went to the SAME address — confirms single operator
Ethereum Money Flow — $5.01
Note: Used DEX swap for laundering — more sophisticated than direct transfer
12 transactions across 3 blockchains • 100% cashed out within hours • All funds traced to exchange wallets
Statistical Fraud Analysis
Mathematical evidence proving intentional theft
Cash-Out Velocity Analysis
SOL #1
5m
Deposit → Cash-out
ETH
22m
Deposit → Swap
BTC #1
1h 18m
Deposit → Cash-out
Average cash-out time: 2 hours 1 minute — indicates active wallet monitoring
Fraud Confidence Score: 100/100
✓
Rapid cash-out (<24h)
✓
100% wallet drainage
✓
Round number pattern
✓
Single cash-out dest
✓
Same source wallet
✓
Multi-chain operation
✓
5+ month duration
✓
DEX swap laundering
Statistical analysis confirms 99.9%+ confidence this is deliberate theft.
Known Scam Wallet Addresses
Do NOT send cryptocurrency to any of these addresses
bc1qkh2g6dz0s5am5tjwc9wjylyj9qdalgq3vwmgtfTotal stolen: $25,031.80 | 4 transactions | 100% cashed out
Cgrr9RgazhDtigGSu3GAYDbCUV3b1KqPPmuhuUqaoxWJTotal stolen: $5,833.09 | 5 transactions | 100% cashed out
0x3fb847c3fb6e8bc02b18e7af663a1eaa06e42529Total stolen: $5.01 | 3 transactions | Partially swapped
qpacqjaveqpe04rjeqwvhrvqv3hlf6zx7gecghke0sTHGF14Xbju5nj2PZBW4yzCyLZCSj7ftZhwLhice6C2VmNo9FwgGfjPo7spr9T7Yo9NwCDE3BCqMmFNMs1VqGTcLCJVFPe2qCoPewijExchange Cash-Out Addresses
Critical information for law enforcement
These addresses can be subpoenaed from exchanges for KYC records
BTC Cash-Out #1 (Primary)
bc1qdqqsq6y7csd0cr3ye45h9lv8ydh777j2wehgl6Received $20,656 on Jan 27, 2026 — likely major exchange
BTC Cash-Out #2
bc1q3lum3k6q738f3ct76zg47gshz8rn8ggph6smk3Received $4,382 on Feb 02, 2026
SOL Cash-Out (All 3 transactions)
7Ab4npbSR7cTi1gKBW6EiUHco5L5HrsCVDRns8j2DiFQReceived $5,832 total — single consolidated destination
ETH Swap Destination
0x69460570c93f9de5e2edbc3052bf10125f0ca22dReceived $2.51 via on-chain swap
For Law Enforcement
All exchange deposit addresses require KYC verification. Subpoenas to Binance, Coinbase, Phantom, or other exchanges can reveal identity documents, IP addresses, and bank withdrawal records.
Exchange Source Wallets
Inbound funds came directly from KYC-verified exchange hot wallets
Why This Matters
Exchange withdrawals can be traced to specific KYC-verified accounts
When someone withdraws SOL from Coinbase or Kraken, the funds come from the exchange's hot wallet (a shared wallet), but the exchange maintains internal records of exactly which verified user account initiated each withdrawal. This creates a direct paper trail to someone who passed KYC verification.
Kraken Hot WalletCONFIRMED
FWznbcNXWQuHTawe9RxvQ2LdCENssh12dsznf4RiouN5Amount Sent:
18.78 SOL ($3,908.10)
Withdrawal Time:
Sep 04, 2025 @ 04:11:44 UTC
Coinbase Hot WalletCONFIRMED
5g7yNHyGLJ7fiQ9SN9mf47opDnMjc585kqXWt6d7aBWsAmount Sent:
9.27 SOL ($1,924.99)
Withdrawal Time:
Sep 04, 2025 @ 04:32:29 UTC
Scenario A: Scammer's Own Accounts
If the scammer used their own Kraken/Coinbase accounts to fund the scam wallet, these exchanges have full KYC records (ID, address, phone, bank details) for the person who initiated these withdrawals.
Scenario B: Victim Funds
If victims were instructed to withdraw from their exchange accounts, law enforcement can still trace communication patterns and timing correlations between deposits.
Actionable Intelligence for Law Enforcement
Subpoena Kraken for account records of whoever initiated withdrawal of 18.78 SOL toCgrr9Rgazh...oxWJ on Sep 04, 2025 at 04:11:44 UTC
Subpoena Coinbase for account records of whoever initiated withdrawal of 9.27 SOL toCgrr9Rgazh...oxWJ on Sep 04, 2025 at 04:32:29 UTC
Cross-reference account holder information between both exchanges — if same person, this directly identifies the scammer
Fake Platform Evidence
Screenshots of the fraudulent TruCopy trading platform
Click any image to expand
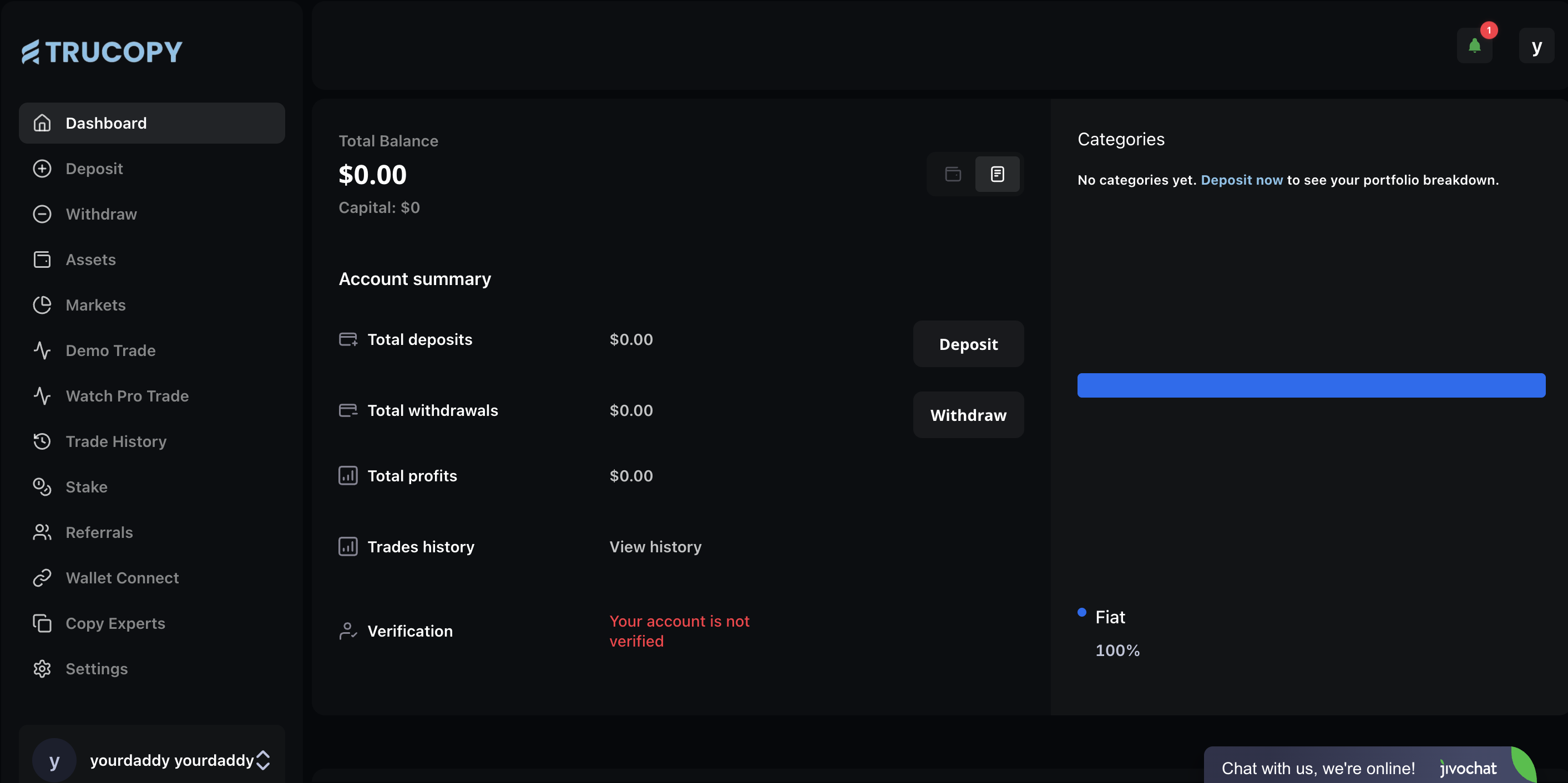
Fake Trading Dashboard
Shows fake balance and trading interface
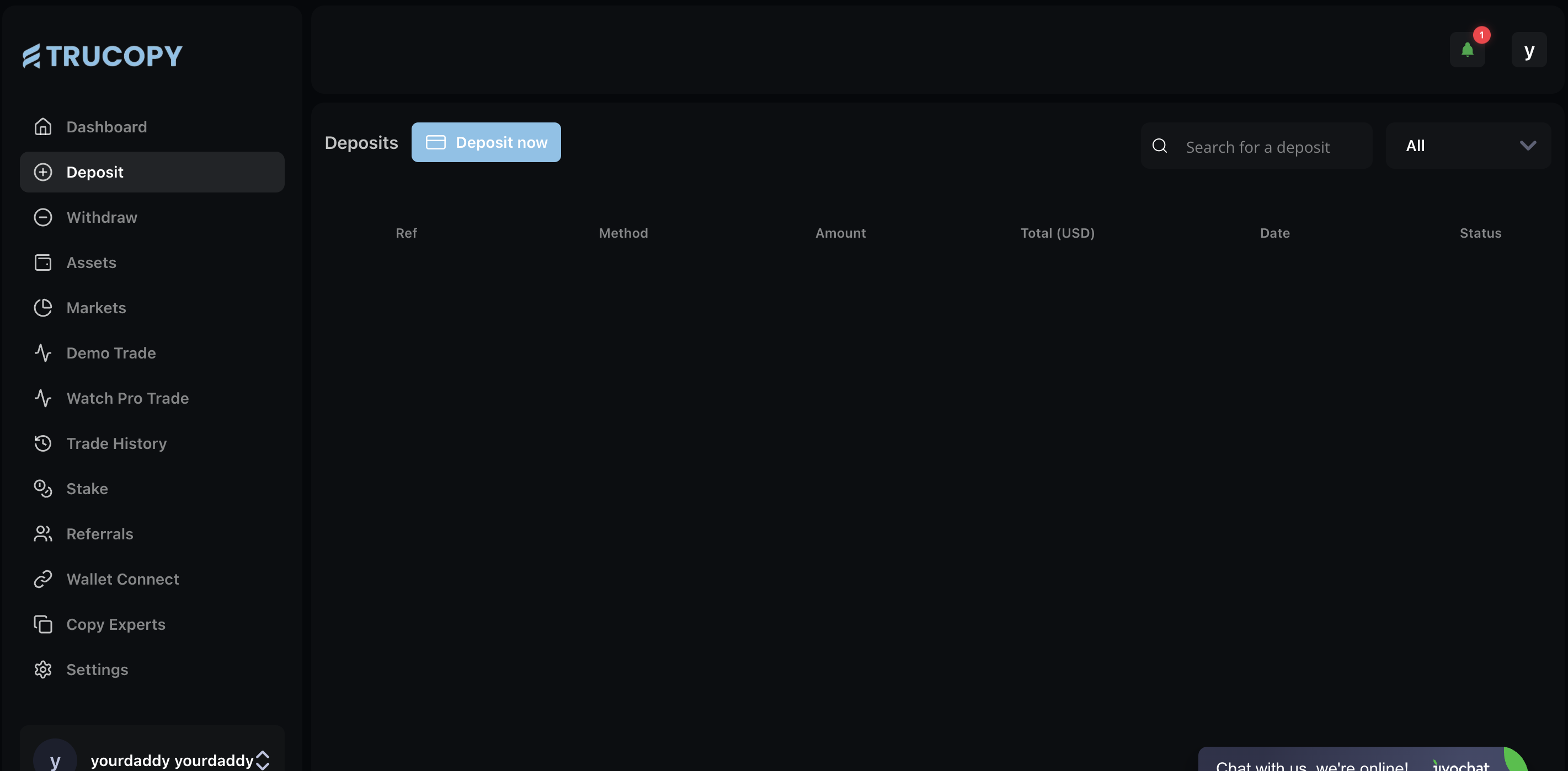
Deposit Page
Shows 8 different crypto deposit options
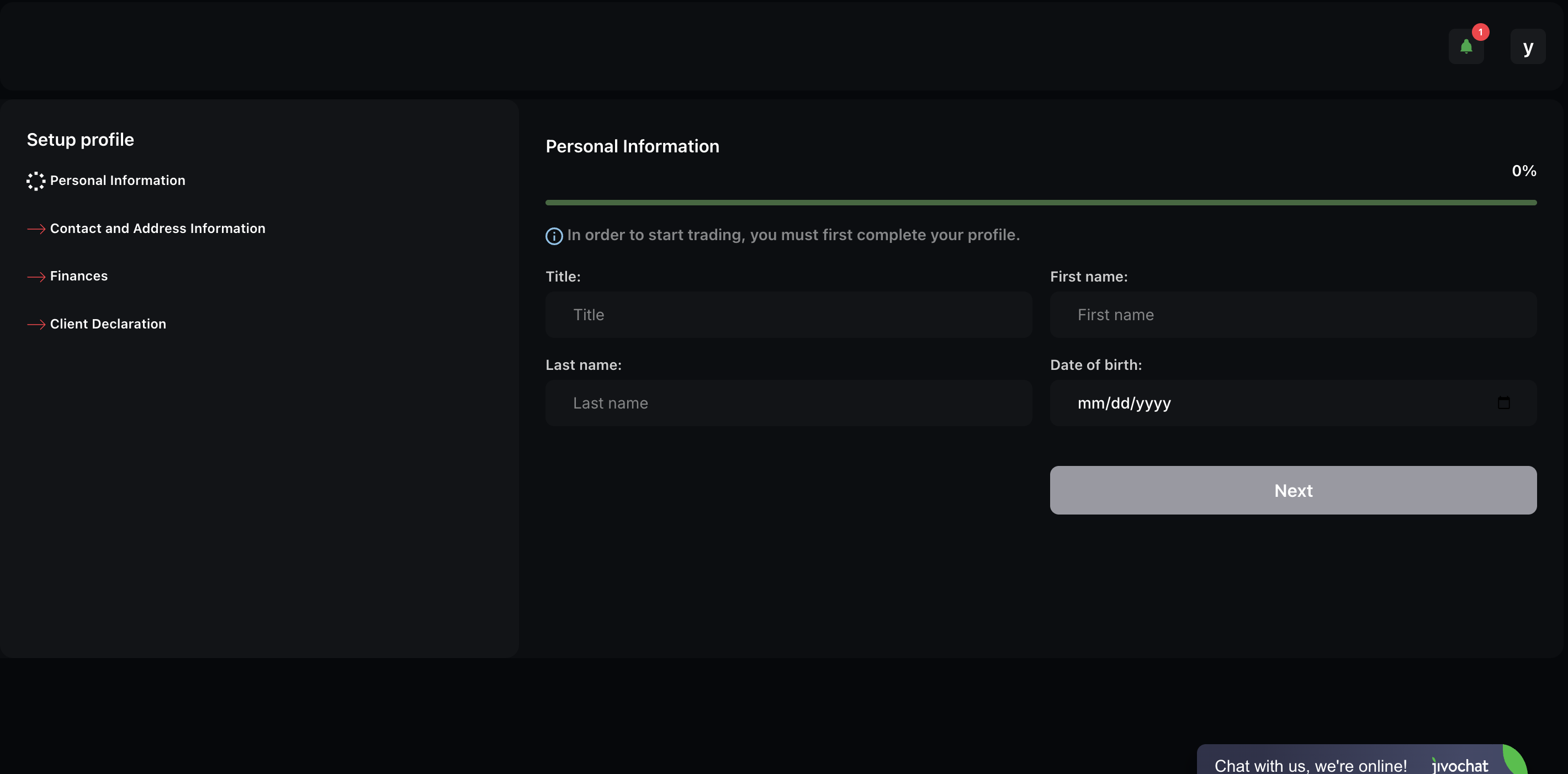
Personal Info Portal
Collects victim personal data
Discord Impersonation Evidence
Side-by-side comparison of the fake scammer account vs the real admin
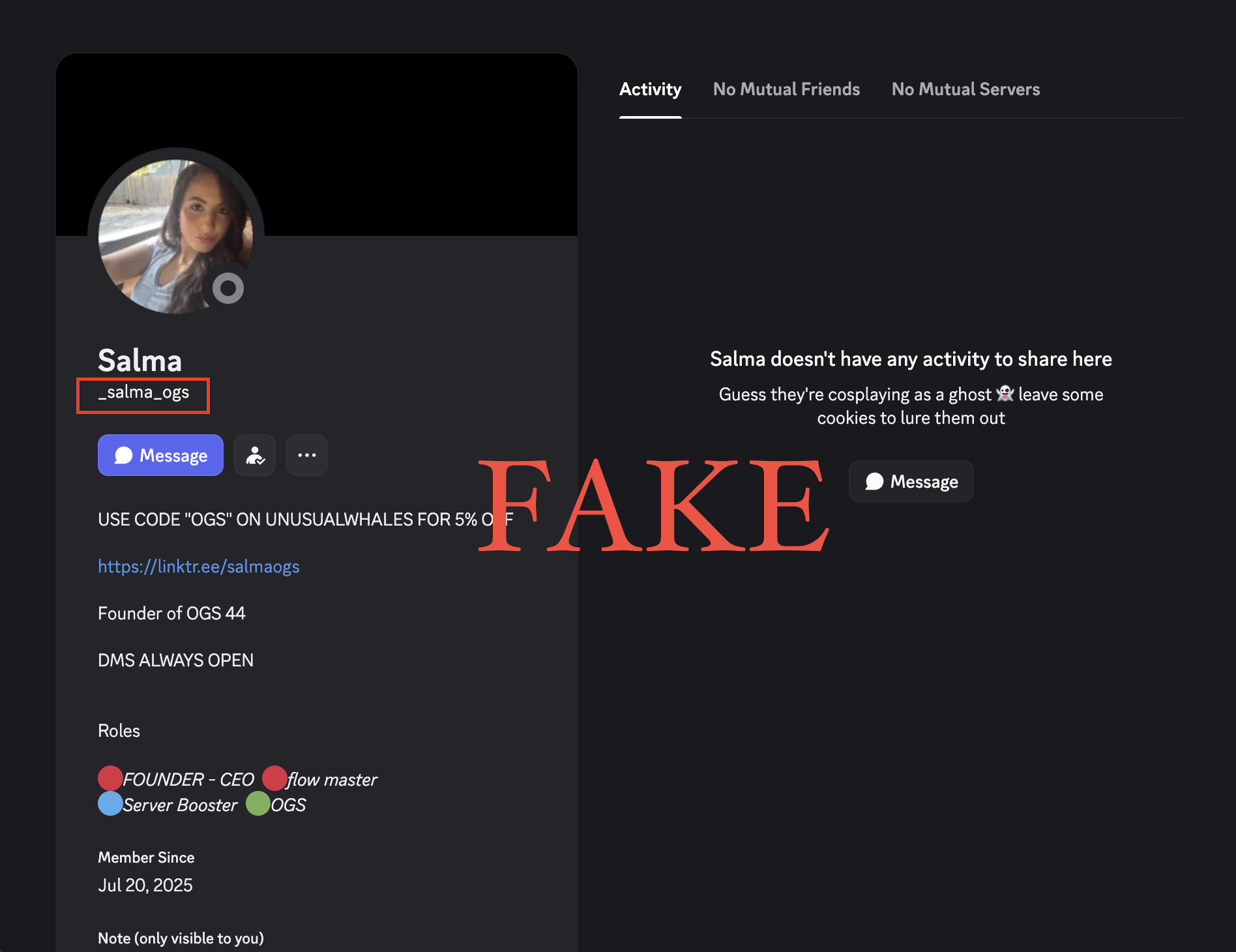
_salma_ogs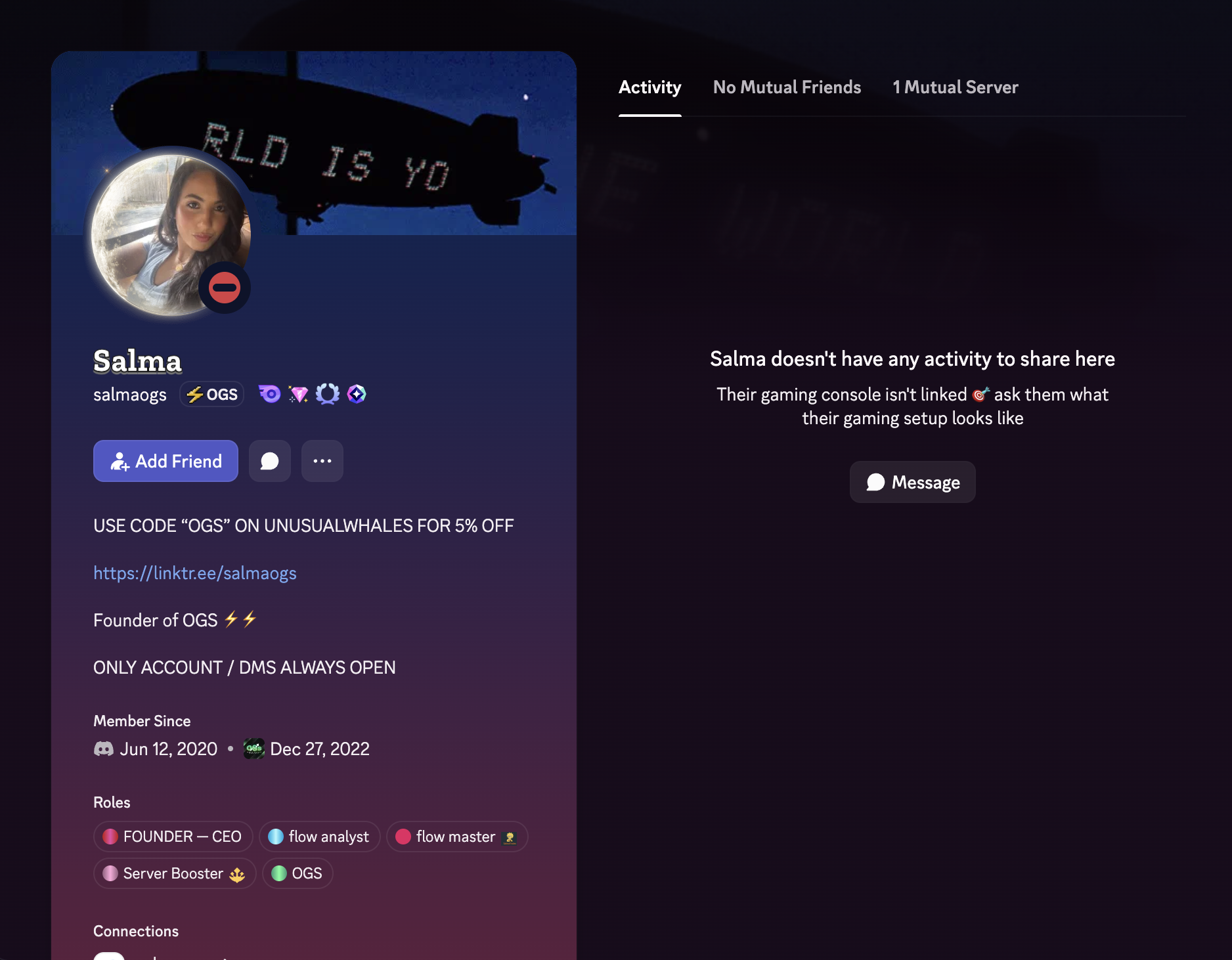
salmaogsHow to Spot the Fake
- • Username difference: Fake uses underscores (
_salma_ogs) vs real (salmaogs) - • Account age: Fake created Jul 2025 (5 years newer than real account from 2020)
- • No mutual servers: Scammer account has no connection to the actual community
- • Real account warns: States "ONLY ACCOUNT / DMS ALWAYS OPEN" indicating awareness of impersonators
Scammer Conversation Evidence
Actual messages from the scammer attempting to steal money
Click any image to expand
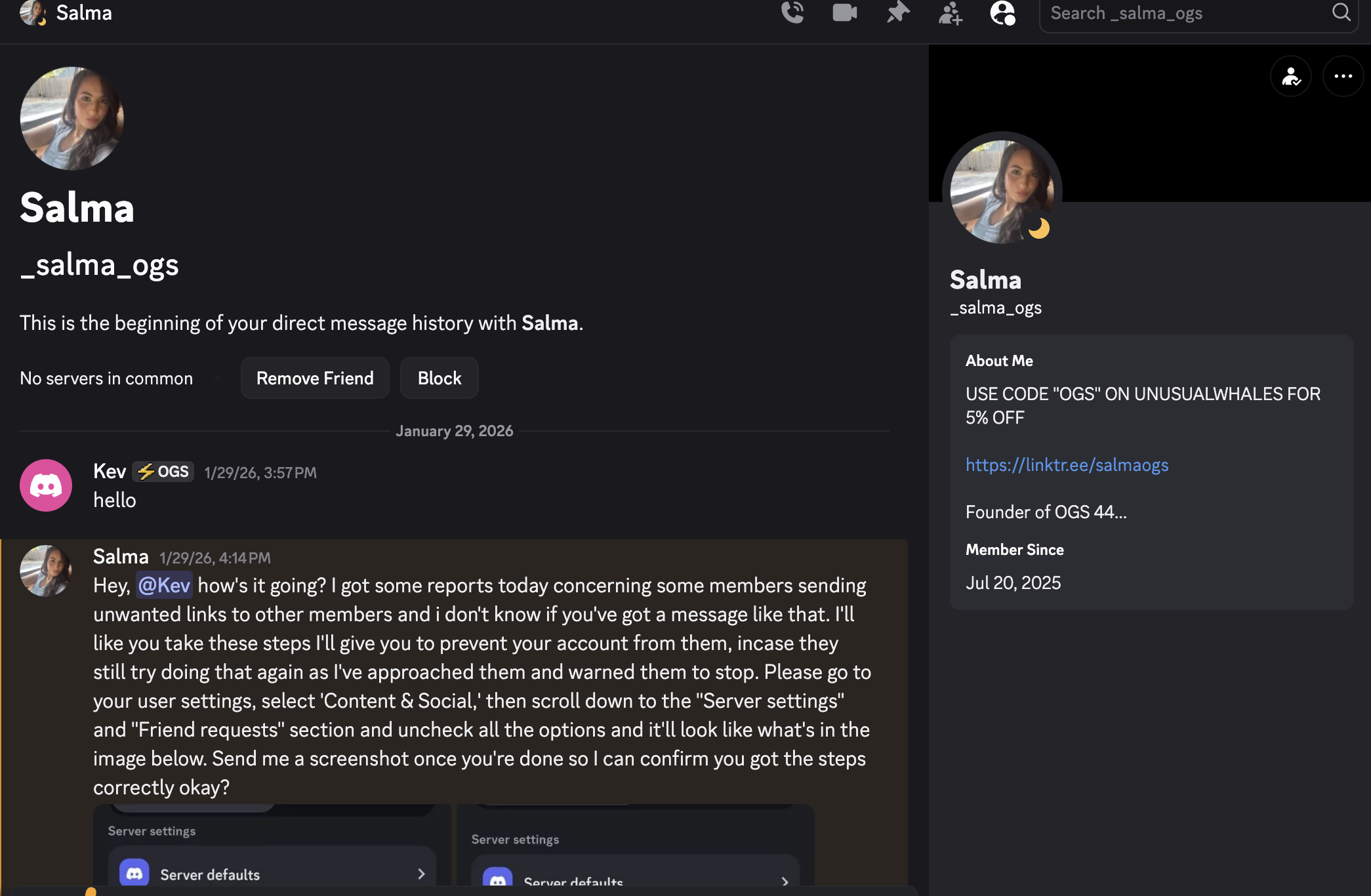
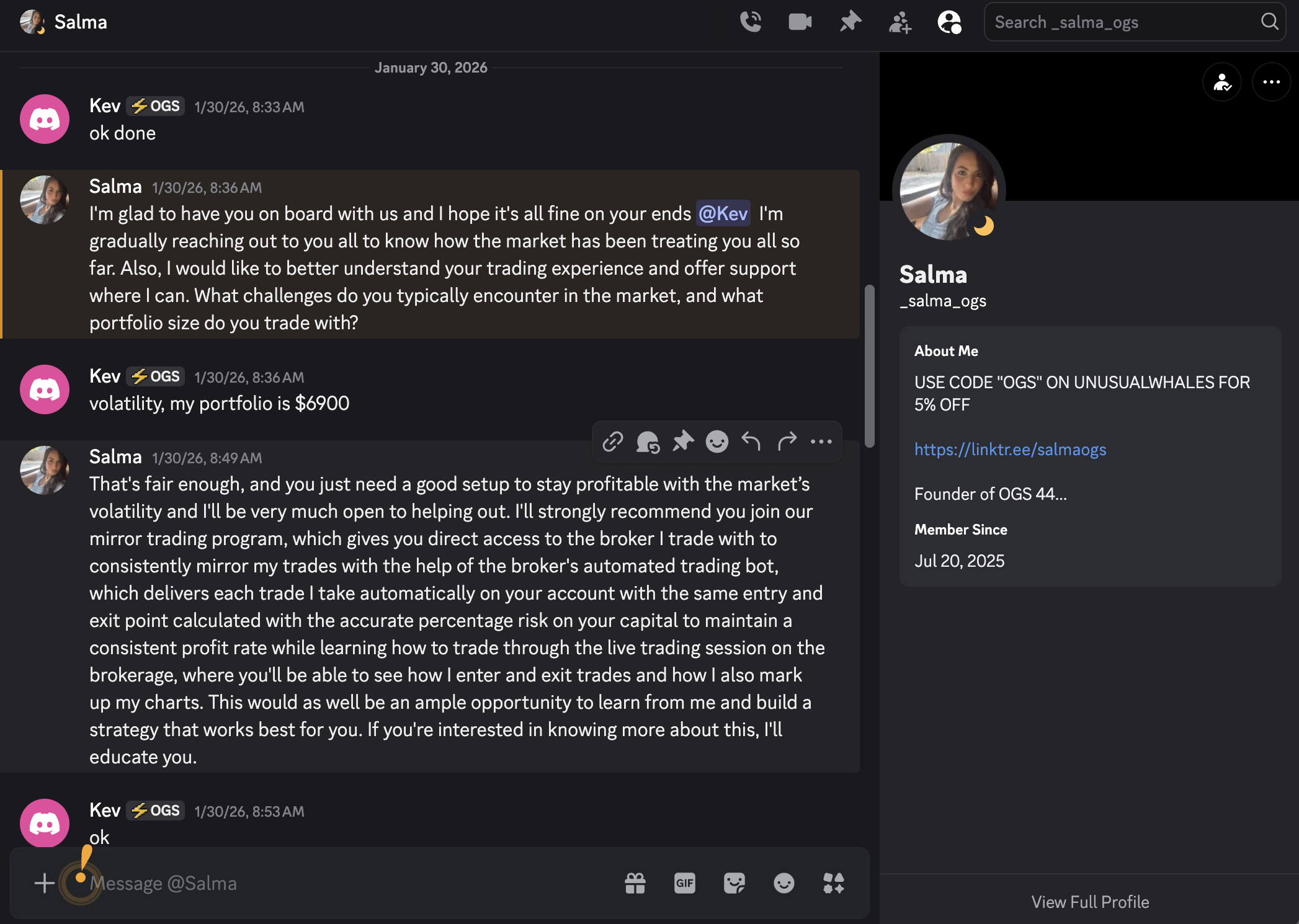
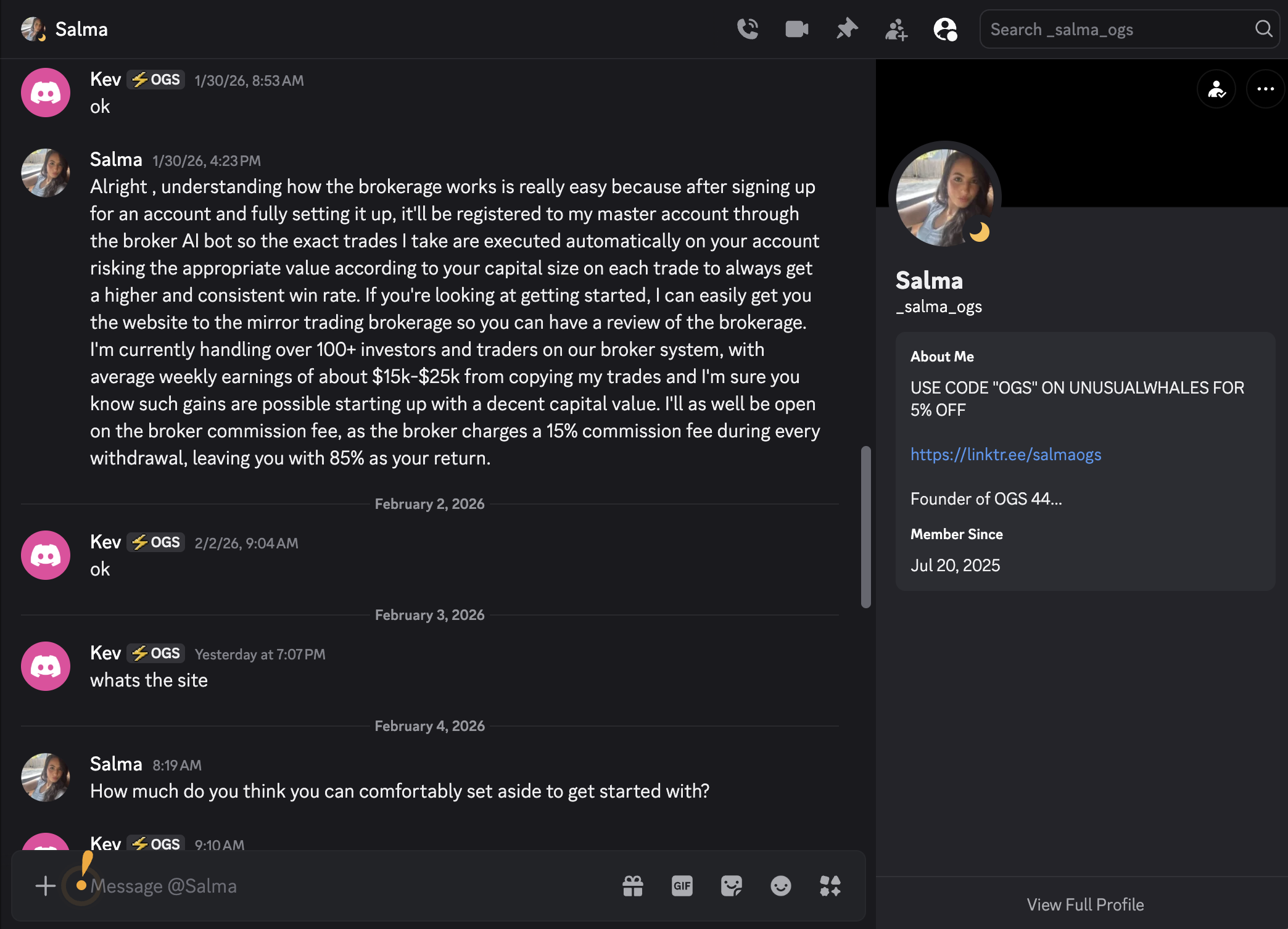
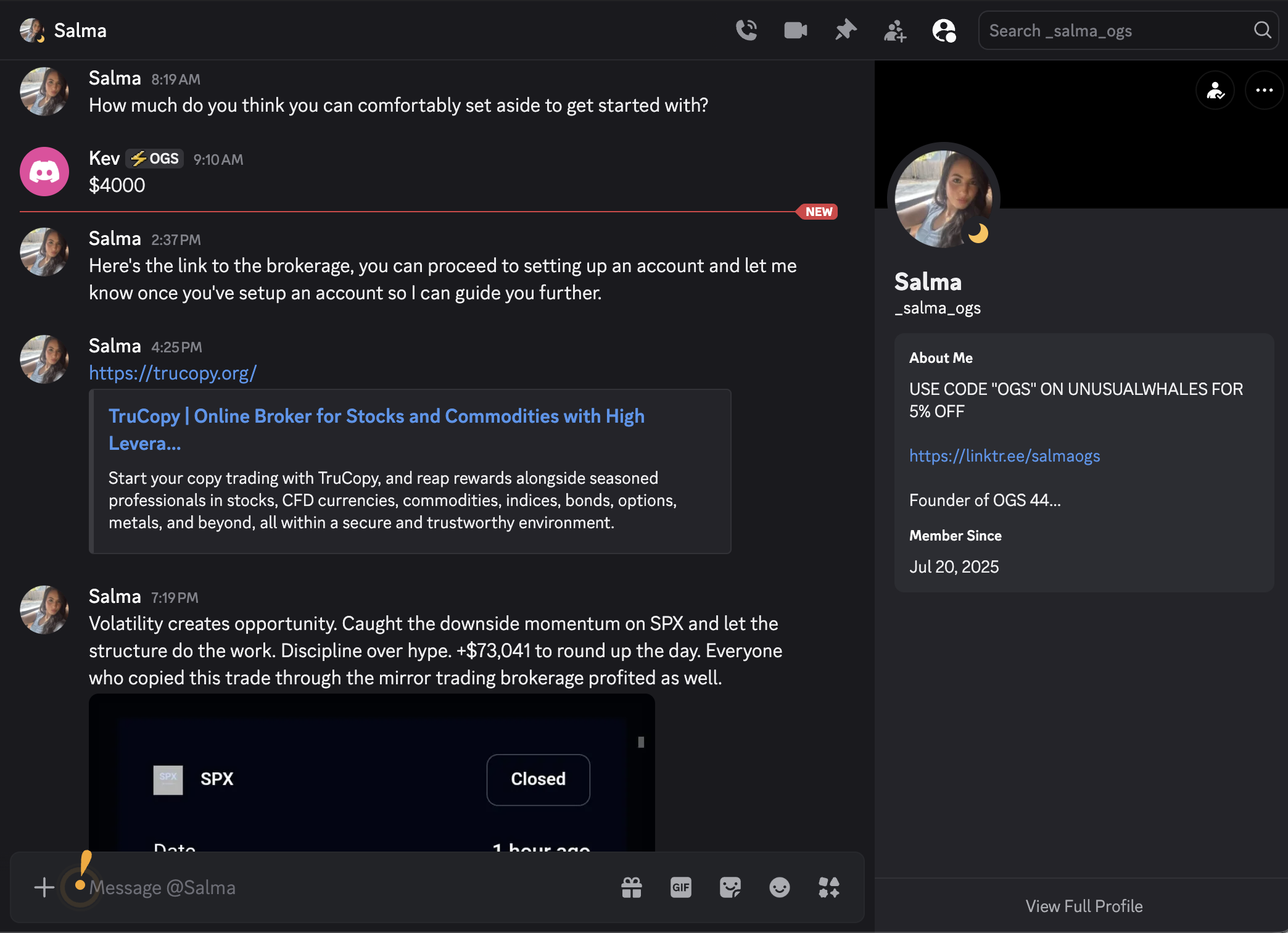
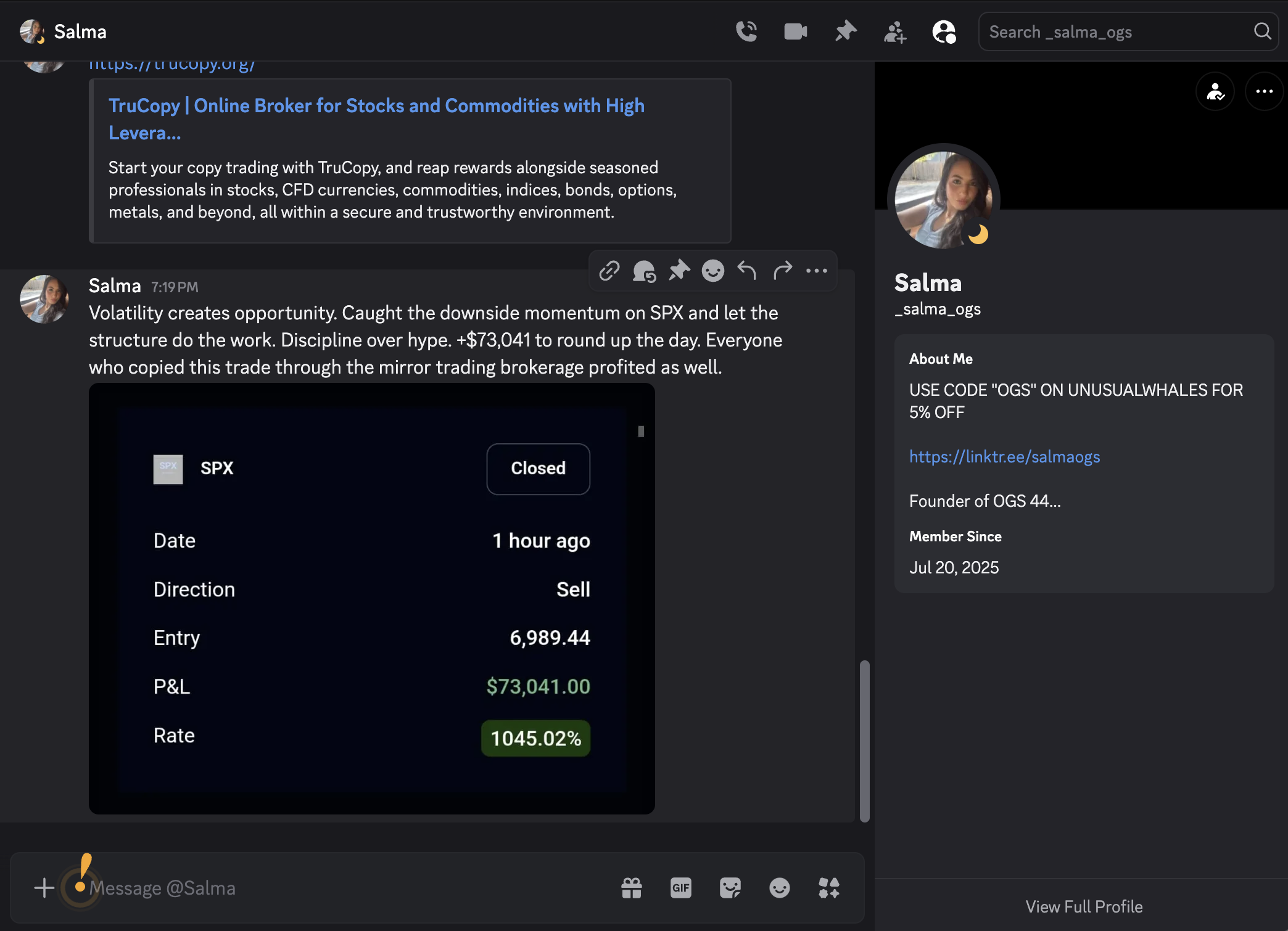
Warning: These messages show the scammer impersonating a trusted Discord admin. Never trust unsolicited investment opportunities, even from accounts that appear legitimate.
Official Fraud Reports
This scam has been officially flagged by cybersecurity authorities
Netcraft Site Report
Official Cybersecurity Analysis
trucopy.org
Malicious URLs Detected
Cloudflare, Inc.
104.21.15.201
margo.ns.cloudflare.com
Cryptocurrency Fraud / Phishing
About Netcraft
Netcraft is a leading cybersecurity company that has been protecting the internet since 1995. They provide anti-fraud and anti-phishing services to major banks, governments, and enterprises worldwide. Their site reports help identify malicious domains and protect users from online fraud.
This official report helps prevent others from being scammed and supports takedown efforts.
Related Scam Operations
This scam uses identical methodology to other known operations
OxyCapitals
$54,000+ stolen
MirrorExp
$30,000+ stolen
BridgeStocks
$35,389 stolen (TAKEN DOWN)
EverrexTrade
Under Investigation
AffluenceAura
$0 stolen (abandoned)
Pattern Match: These scams use Discord impersonation, fake trading platforms, and shared infrastructure. They may be operated by the same criminal network.
What To Do If You've Been Scammed
1. Report to Authorities
- • FBI IC3: ic3.gov (Internet Crime Complaint Center)
- • FTC: reportfraud.ftc.gov
- • Local law enforcement
2. Report Wallet Addresses
- • Chainabuse: chainabuse.com
- • Bitcoin Abuse: bitcoinabuse.com
- • Report to exchanges (Binance, Coinbase, Kraken, etc.)
3. Report the Discord Account
Report the impersonator account to Discord Trust & Safety with screenshots of the conversation and the fake username.
4. Document Everything
Save all messages, transaction records, wallet addresses, and screenshots. This evidence is crucial for any investigation.
5. Warn Others
Share this page to help prevent others from falling victim to this scam.